X509 Public Key Certificate Generate
- Windows Generate X509 Certificate
- Create Self Signed X509 Certificate
- Create X509 Certificate
- X509 Public Key Certificate Generate Download
- X509 Public Key Certificate Generate Pdf
- In One Sentence: What is a Certificate?
- What Applications use Certificates?
- How do I get a Certificate?
- What is Inside an X.509 Certificate?
- What Java API Can Be Used to Access and Manage Certificates?
- What Java Tool Can Generate, Display, Import, and Export X.509 Certificates?
A public-key certificate is a digitally signed statement from one entity, saying that the public key (and some other information) of another entity has some specific value.
Let us expand on some of the key terms used in this sentence:

- Public Keys
- These are numbers associated with a particular entity, and are intended to be known to everyone who needs to have trusted interactions with that entity. Public keys are used to verify signatures.
- Digitally Signed
- If some data is digitally signed it has been stored with the 'identity' of an entity, and a signature that proves that entity knows about the data. The data is rendered unforgeable by signing with the entitys' private key.
- Identity
- A known way of addressing an entity. In some systems the identity is the public key, in others it can be anything from a Unix UID to an Email address to an X.509 Distinguished Name.
- Signature
- A signature is computed over some data using the private key of an entity (the signer).
- Private Keys
- These are numbers, each of which is supposed to be known only to the particular entity whose private key it is (that is, it's supposed to be kept secret). Private and public keys exist in pairs in all public key cryptography systems (also referred to as 'public key crypto systems'). In a typical public key crypto system, such as DSA, a private key corresponds to exactly one public key. Private keys are used to compute signatures.
- Entity
- An entity is a person, organization, program, computer, business, bank, or something else you are trusting to some degree.
Basically, public key cryptography requires access to users' public keys. In a large-scale networked environment it is impossible to guarantee that prior relationships between communicating entities have been established or that a trusted repository exists with all used public keys. Certificates were invented as a solution to this public key distribution problem. Now a Certification Authority (CA) can act as a Trusted Third Party. CAs are entities (e.g., businesses) that are trusted to sign (issue) certificates for other entities. It is assumed that CAs will only create valid and reliable certificates as they are bound by legal agreements. There are many public Certification Authorities, such as VeriSign, Thawte, Entrust, and so on. You can also run your own Certification Authority using products such as the Netscape/Microsoft Certificate Servers or the Entrust CA product for your organization.
Dec 01, 2015 A public key is the one that is released to the public. It allows anyone to use it for encrypting messages to be sent to the user, as well as for decrypting messages received from the user. F you use OpenSSL to generate certificates, the private key will contain public key information, therefore the public key does not have to be generated. The private key is kept secret. The public key is typically embedded in a binary certificate, and the certificate is published to a database that can be reached by all authorized users. The X.509 public key infrastructure (PKI) standard identifies the requirements for robust public key certificates. Jun 29, 2017 $ openssl x509 -in cert.pem -outform der -out cert.der. And $ openssl x509 -in cert.der -inform der -outform pem -out cert.pem. The PKCS#12 and PFX formats can be converted with the following commands. PFX (private key and certificate) to PEM (private key and certificate): $ openssl pkcs12 -in keyStore.pfx -out keyStore.pem -nodes. This certificate request will be 'send' to the certificate authority which can then chose to accept it and generate a signed certificate from it. To generate a certificate request, type the following command: openssl req -new -sha1 -key alice.key -out alice.csr Fill all the certificate request attributes. This will generate a file named alice.
Probably the most widely visible application of X.509 certificates today is in web browsers (such as Mozilla Firefox and Microsoft Internet Explorer) that support the TLS protocol. TLS (Transport Layer Security) is a security protocol that provides privacy and authentication for your network traffic. These browsers can only use this protocol with web servers that support TLS.
Other technologies that rely on X.509 certificates include:
- Various code-signing schemes, such as signed Java ARchives, and Microsoft Authenticode.
- Various secure E-Mail standards, such as PEM and S/MIME.
- E-Commerce protocols, such as SET.
There are two basic techniques used to get certificates:
- you can create one yourself (using the right tools, such as keytool), or
- you can ask a Certification Authority to issue you one (either directly or using a tool such as keytool to generate the request).
- Matched public and private keys, generated using some special tools (such as keytool), or a browser. Only the public key is ever shown to anyone else. The private key is used to sign data; if someone knows your private key, they can masquerade as you .. perhaps forging legal documents attributed to you!
- You need to provide information about the entity being certified (e.g., you). This normally includes information such as your name and organizational address. If you ask a CA to issue a certificate for you, you will normally need to provide proof to show correctness of the information.
If you are asking a CA to issue you a certificate, you provide your public key and some information about you. You'll use a tool (such as keytool or a browser that supports Certificate Signing Request generation). to digitally sign this information, and send it to the CA. The CA will then generate the certificate and return it.
If you're generating the certificate yourself, you'll take that same information, add a little more (dates during which the certificate is valid, a serial number), and just create the certificate using some tool (such as keytool). Not everyone will accept self-signed certificates; one part of the value provided by a CA is to serve as a neutral and trusted introduction service, based in part on their verification requirements, which are openly published in their Certification Service Practices (CSP).
The X.509 standard defines what information can go into a certificate, and describes how to write it down (the data format). All X.509 certificates have the following data, in addition to the signature:
- Version
- This identifies which version of the X.509 standard applies to this certificate, which affects what information can be specified in it. Thus far, three versions are defined.
- Serial Number
- The entity that created the certificate is responsible for assigning it a serial number to distinguish it from other certificates it issues. This information is used in numerous ways, for example when a certificate is revoked its serial number is placed in a Certificate Revocation List (CRL).
- Signature Algorithm Identifier
- This identifies the algorithm used by the CA to sign the certificate.
- Issuer Name
- The X.500 name of the entity that signed the certificate. This is normally a CA. Using this certificate implies trusting the entity that signed this certificate. (Note that in some cases, such as root or top-level CA certificates, the issuer signs its own certificate.)
- Validity Period
- Each certificate is valid only for a limited amount of time. This period is described by a start date and time and an end date and time, and can be as short as a few seconds or almost as long as a century. The validity period chosen depends on a number of factors, such as the strength of the private key used to sign the certificate or the amount one is willing to pay for a certificate. This is the expected period that entities can rely on the public value, if the associated private key has not been compromised.
- Subject Name
- The name of the entity whose public key the certificate identifies. This name uses the X.500 standard, so it is intended to be unique across the Internet. This is the Distinguished Name (DN) of the entity, for example, (These refer to the subject's Common Name, Organizational Unit, Organization, and Country.)
- Subject Public Key Information
- This is the public key of the entity being named, together with an algorithm identifier which specifies which public key crypto system this key belongs to and any associated key parameters.
X.509 Version 1 has been available since 1988, is widely deployed, and is the most generic.
X.509 Version 2 introduced the concept of subject and issuer unique identifiers to handle the possibility of reuse of subject and/or issuer names over time. Most certificate profile documents strongly recommend that names not be reused, and that certificates should not make use of unique identifiers. Version 2 certificates are not widely used.
X.509 Version 3 is the most recent (1996) and supports the notion of extensions, whereby anyone can define an extension and include it in the certificate. Some common extensions in use today are: KeyUsage (limits the use of the keys to particular purposes such as 'signing-only') and AlternativeNames (allows other identities to also be associated with this public key, e.g. DNS names, Email addresses, IP addresses). Extensions can be marked critical to indicate that the extension should be checked and enforced/used. For example, if a certificate has the KeyUsage extension marked critical and set to 'keyCertSign' then if this certificate is presented during SSL communication, it should be rejected, as the certificate extension indicates that the associated private key should only be used for signing certificates and not for SSL use.
All the data in a certificate is encoded using two related standards called ASN.1/DER. Abstract Syntax Notation 1 describes data. The Definite Encoding Rules describe a single way to store and transfer that data. People have been known to describe this combination simultaneously as 'powerful and flexible' and as 'cryptic and awkward'.
The IETF PKIX working group is in the process of defining standards for the Internet Public Key Infrastructure. We are closely following their work, and support the X.509 Certificate and CRL Profile, which is specified in RFC 3280.
The Certificate API, found in thejava.security.cert package, includes the following: - the CertificateFactory class defines the functionality of a certificate factory, which is used to generate certificate, certificate revocation list (CRL), and certification path objects from their encoding.
- the Certificate class is an abstract class for managing a variety of certificates. It is an abstraction for certificates that have different formats but important common uses. For example, different types of certificates, such as X.509 and PGP, share general certificate functionality (like encoding and verifying) and some types of information like public key.
- the CRL class is an abstract class for managing a variety of Certificate Revocation Lists (CRLs).
- the X509Certificate class is an abstract class for X.509 Certificates. It provides a standard way to access all the attributes of an X.509 certificate.
- the X509Extension interface is an interface for an X.509 extension. The extensions defined for X.509 v3 certificates and v2 CRLs (Certificate Revocation Lists) provide mechanisms for associating additional attributes with users or public keys, such as for managing the certification hierarchy, and for managing CRL distribution.
- the X509CRL class is an abstract class for an X.509 Certificate Revocation List (CRL). A CRL is a time-stamped list identifying revoked certificates. It is signed by a Certification Authority (CA) and made freely available in a public repository.
- the X509CRLEntry class is an abstract class for a CRL entry.
Windows Generate X509 Certificate
A keystore is a protected database that holds keys and certificates. Access to a keystore is guarded by a password (defined at the time the keystore is created, by the person who creates the keystore, and changeable only when providing the current password). In addition, each private key in a keystore can be guarded by its own password.
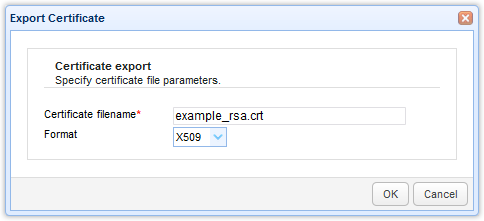
Using keytool, it is possible to display, import, and export X.509 v1, v2, and v3 certificates stored as files, and to generate new self-signed v3 certificates. For examples, see the 'EXAMPLES' section of the keytool documentation ( for Solaris ) ( for Windows ).
Freelan relies on X509 certification for its authentication mechanism. For several hosts to connect using freelan, each and everyone of them will have to have his unique certificate.
Certificate generation is a very sensitive topic that must not be taken lightly, and I encourage you to read a lot about it and to fully understand its principles before you continue.
To generate certificates, you will need the openssl command line tool. Make sure it is in your PATH so that you can execute it from anywhere.
A freelan host (also called 'contact') identifies himself by presenting a X509 certificate to other hosts. This certificate is public. One can give it to anyone without facing security issues.
This certificate contains a public RSA key which anyone can read and use and, amongst other things, a common name which can be anything from an email address to a hostname: this common name identifies the host and should be unique inside the virtual private network.
Associated with this certificate is a private key. As its name implies, the private key is private and MUST remain so ! I cannot stress that enough: Never give your private key to anyone ! Don't store it on your desktop. Don't send it in cleartext to your email account. Don't make a t-shirt out of it.
If you are curious about why we need those two elements, here is a short explanation:
- If someone uses the public key to cipher something, only the owner of the private key can decipher it. That is, you have the guarantee that when a message is sent, only the intended recipient can read it.
- If someone uses its private key to 'cipher' (actually, 'sign') something, anybody with the associated public key can read it. That is, you have the guarantee that when a message is received, its emitter is really who he claims to be and that the message was not altered during the transmission.
Those two principles are sufficient to ensure both authenticity and confidentiality but have a cost: you have to generate the private keys and the certificates first.
While certificates give us authenticity and confidentiality, anyone can generate a certificate containing wrong information (an incorrect 'common name' for instance) and so we have to check every certificate we were given, and to ensure that they really were emitted by the people or the organization they refer to. Those verifications are really time consuming.
Luckily enough, X509 contains a mechanism to ease this which is called certificate signing.
Any X509 certificate can be signed by another certificate called a parent certificate. This signature is generated with the private key associated with the parent certificate and guarantees that the signed certificate was verified by the people that own the parent certificate (also called a certificate authority).
That is, with this mechanism, one doesn't have to trust directly every possible certificate, but only the parent certificates. It is worth saying that this makes the parent private keys even more sensitive !
Note: The parent certificate can also be signed by an even higher parent certificate. This is often referred to as a certificate chain.
Good ? Let's create certificates !
Here are the steps to create a simple certificate authority.
Get the certificate authority sample folder archive and extract it where you like.
Go inside the extracted folder and type:
When prompted for a passphrase, type what you want, but remember it ! You will have to type it whenever the certificate authority private key file will be needed.
May 19, 2017 God of War III Serial Key Download Code Crack key generator Full Game Torrent skidrow Origin Key and Steam Online Code Avaiable. God of War III Serial Key Cd Key Free Download Crack Full Game God of War III Serial Cd Key Generator License Activator Product. Jun 18, 2018 God Of War 3 PC Game Free Download:-CrackSoftPC.Com – Today we are uploading a very well know and most played game God Of War 3 PC Game Free Download.God Of War 3 Free Download is an award-winning game of the year 2012. God of War Was released for a third-person action game. The main thing about this game is its Best graphics. Oct 06, 2019 Download Setup God Of War 3 Pc Cd Key + Crack Free Download. Anyone who exactly wants to enjoy playing in the God of War series without having to pay genuine authentic serial codes for this, we now offer you the possibility to find just a game for free. GOD OF WAR 3 DOWNLOAD PC GAME COMPRESSED SETUP Download God OF War-3 PC Game full version highly compressed.Compressed installatio. God Of War 3 Free Download Full PC Game FULL VERSION. We Have Provided Direct Links Full Setup Of This Game. This game starts with an outstanding storyline afterward he tears off the head of Helios which is great after that he ripped off the leg of Hermes from the body and in the end, he punches the false god named Zeus. God of war 3 key generator and full game download.
You should now have a certificate file at crt/ca.crt and its associated private key file at key/ca.key.
Now that you have a working certificate authority, it is time to generate client certificates. Repeat the following step for every certificate/private key pair you need.
Private key generation
The first step is to generate a private key:
If you wish to protect your private key with a passphrase, use the following command line instead:
Note: Using a passphrase will increase the security of your private key. Even if it gets stolen, the password will be required to use the private key. However, setting a passphrase on the private key can prevent its use in automated systems.
This will generate a file named alice.key. This is the client private key.
Note: every host should generate its own private key to keep it secret. The certificate authority does not need the client private key to sign the client certificate.
Issuing a certificate request
Create Self Signed X509 Certificate
Now that a client has a private key, it must generate a certificate request out of it. This certificate request will be 'send' to the certificate authority which can then chose to accept it and generate a signed certificate from it.
To generate a certificate request, type the following command:
Fill all the certificate request attributes.
Create X509 Certificate
This will generate a file named alice.csr. This is the client certificate request.
Note: Those two steps (private key and certificate request generation) do NOT need to be done in the certificate authority folder. Actually, they should even be done on the final host directly for privacy's sake.
Generating a signed certificate from a certificate request
X509 Public Key Certificate Generate Download
The final step is to generated a signed certificate from the certificate request. This is obviously done on the CA.
Type the following command:
X509 Public Key Certificate Generate Pdf
This will prompt for the ca.key passphrase then ask you whether you want to accept the certificate request.
This will generate a alice.crt file: the client signed certificate which can be send to anyone.
Repeat these steps for every client, and you will be ready to use freelan ! Congratulations !